The Big Four hyperscalers spent a record $725 billion on AI infrastructure in Q1 2026, sparking debates on future revenue and profitability impacts.
The Latest
The $725 Billion Question: Hyperscaler Capex Q1 2026 and What the Earnings Don’t Answer
The Compute Reckoning: Anthropic Finally Admits What Customers Suspected for Ten Months
Anthropic confirms that compute shortages led to recent customer experience issues, with a major deal with SpaceX signaling a strategic shift.
The NVIDIA Earnings Preview: What Q1 FY27 Will Reveal About the AI Cycle
NVIDIA reports Q1 FY27 earnings on May 20, 2026. Key focus on revenue, demand signals, and AI infrastructure health amid a trillion-dollar order backlog.
The Anthropic-Blackstone-Goldman JV: Reverse-Engineering the $1.5B Enterprise AI Services Structure
Anthropic, Blackstone, and Goldman Sachs launched a $1.5 billion standalone AI services firm to target mid-sized companies, embedding Anthropic engineers directly.
The Google I/O 2026 Preview: What May 19-20 Will Reveal About Google’s Agentic Bet
Preview of Google I/O 2026 focusing on expected reveals about Google’s agentic AI, Gemini 4.0, and related infrastructure developments on May 19-20.
Forward-Deployed: The Integration Wall, and the Role That Now Pays $700K to Climb It
Forward-Deployed Engineers now command up to $700K in total compensation, transforming enterprise AI deployment and surpassing traditional roles in tech.
The Memento Constraint: Why Continual Learning Is the Trillion-Dollar Bottleneck Nobody Is Pricing
Exploring how the inability of current AI models to learn continually limits enterprise AI and the potential economic impact of solving this challenge.
The Enforcement Countdown: 89 Days Until the EU AI Act’s GPAI Penalty Phase Begins
The EU AI Act’s enforcement powers for GPAI providers activate on August 2, 2026, marking a key compliance deadline for AI companies operating in Europe.
7 Best Office Whiteboard System for Startup Planning in 2026
Discover the top office whiteboard systems for startup planning in 2026. Find the best options for productivity, budgeting, and team collaboration.
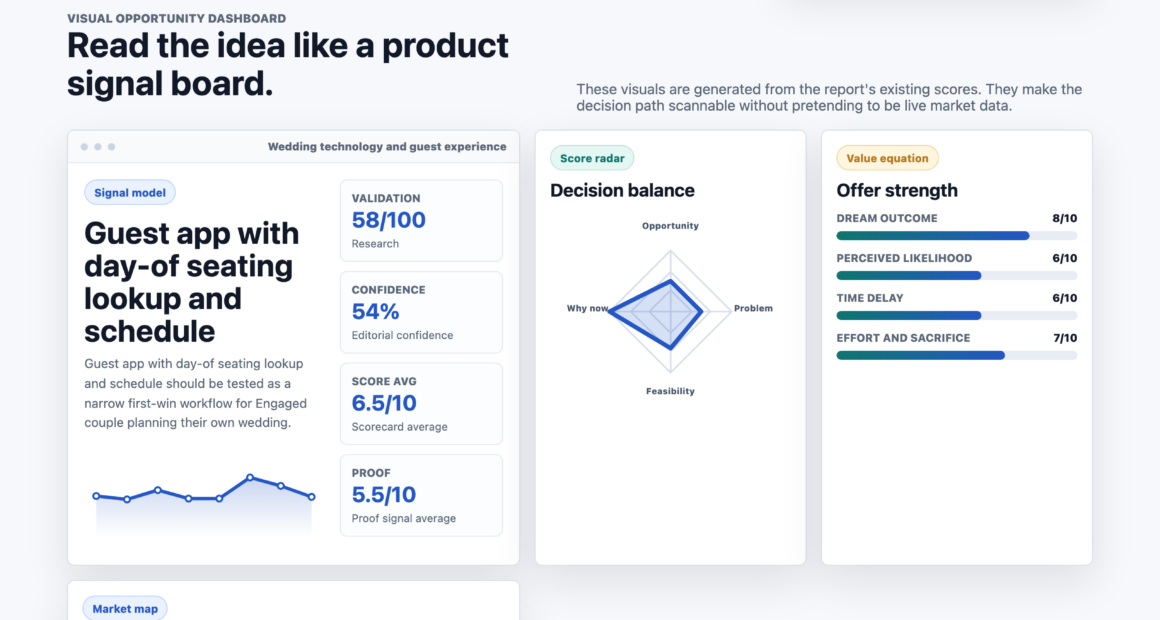
Guest app with day-of seating lookup and schedule
A new guest app allows wedding attendees to check their seating and schedule via a shared link, aiming to reduce last-minute questions for couples.